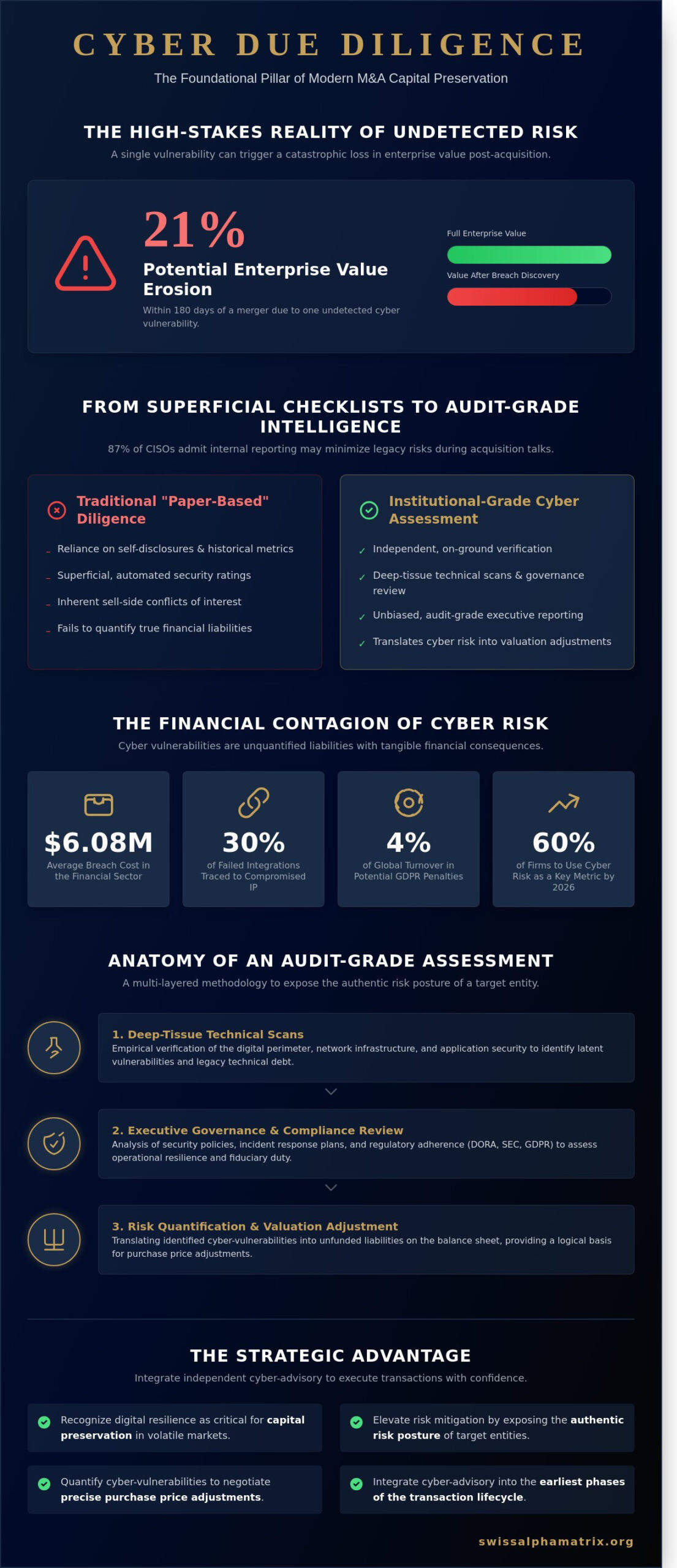
A single undetected vulnerability within a target’s digital infrastructure can erode over 21% of a firm’s enterprise value within 180 days of a merger, according to recent analysis of global tech-sector transactions. You’re likely aware that the traditional reliance on financial audits and historical performance metrics provides an incomplete picture of an asset’s true risk profile in our interconnected global market. For the sophisticated investor, conducting rigorous cybersecurity due diligence isn’t merely a technical box to check; it’s a foundational pillar of modern capital preservation. It’s a strategic necessity to ensure that the alpha you’ve identified isn’t compromised by legacy technical debt or undisclosed breaches.
We’ll provide you with a bespoke, executive-level framework designed to identify hidden liabilities and translate abstract cyber risks into concrete valuation adjustments. This institutional-grade approach ensures that your deal negotiations and indemnity clauses are informed by a precise understanding of the target’s security posture. By the end of this exploration, you’ll possess the strategic architecture necessary to execute high-stakes M&A with the quiet confidence that characterizes the highest echelons of Swiss financial tradition. We’ll examine how to move from superficial checklists to an audit-grade assessment that protects your long-term asset value.
Key Takeaways
- Recognize how the shifting strategic landscape of 2026 necessitates an institutional-grade investigation into a target’s digital resilience to ensure the preservation of capital within volatile global markets.
- Elevate your transactional risk mitigation by implementing a rigorous cybersecurity due diligence framework that moves beyond superficial self-disclosures to expose the authentic risk posture of a target entity.
- Learn to quantify identified cyber-vulnerabilities as unfunded liabilities on the balance sheet, providing a logical mechanism for negotiating precise purchase price adjustments.
- Distinguish between generic, automated security ratings and bespoke, executive-led intelligence that prioritizes on-ground verification for complex, cross-border financial programmes.
- Integrate independent cyber-advisory into the earliest phases of the transaction lifecycle to circumvent the inherent conflicts of interest found in traditional sell-side disclosures.
The Strategic Imperative: Cybersecurity Due Diligence in 2026
The pursuit of alpha in the modern era necessitates a granular understanding of the digital substrate upon which all value is built. Within the complex architecture of global mergers and acquisitions, the traditional due diligence process has evolved into a sophisticated, multi-layered assessment of digital integrity. Cybersecurity due diligence is now defined as the institutional-grade investigation of a target’s digital resilience and risk posture, serving as a primary driver of deal success in volatile global markets. By Q1 2026, industry benchmarks suggest that 60% of organizations will utilize cybersecurity risk as a fundamental metric for evaluating third-party transactions. This transition from a rudimentary ‘IT checklist’ to a model of ‘Executive Intelligence’ reflects the reality that technical vulnerabilities are, in essence, unquantified financial liabilities.
Seasoned investors understand that internal reports often suffer from institutional bias, which is why independent advisory has become a prerequisite for high-stakes transactions. Providing unbiased, audit-grade reporting allows stakeholders to visualize the target’s security maturity without the filter of corporate optimism. It’s a strategic necessity that mirrors the discretion and precision of Swiss private banking traditions, ensuring that the capital remains protected against unforeseen digital contingencies. This level of scrutiny isn’t merely about identifying flaws; it’s about the strategic calibration of risk-adjusted returns in an environment where a single breach can negate years of projected growth.
Capital Protection in the Digital Age
Undisclosed data breaches act as a corrosive force, often eroding asset value long after the initial acquisition is finalized. A 2024 analysis by IBM indicated that breach-related costs in the financial sector averaged $6.08 million per incident, yet the ‘contagion risk’, where a target’s latent vulnerabilities compromise the acquirer’s entire ecosystem, poses a far greater existential threat. During cross-border transfers, the protection of intellectual property becomes the central pillar of value preservation. This is particularly critical when 30% of failed integrations are traced back to compromised proprietary data or stolen trade secrets that were extracted during the pre-deal phase.
Regulatory and Compliance Mandates
The current regulatory environment, defined by rigorous mandates such as the Digital Operational Resilience Act (DORA) and SEC cyber-disclosure rules, has removed the margin for error in corporate oversight. Directors and officers face significant personal liability; failing to conduct rigorous cybersecurity due diligence is increasingly viewed as a breach of fiduciary duty. Independent validation provides a robust defense, establishing ‘safe harbour’ protections during regulatory audits. This proactive stance potentially mitigates penalties that, under GDPR mandates, can reach 4% of a firm’s global annual turnover, ensuring that compliance remains a pillar of the firm’s broader commitment to excellence and integrity.
The Anatomy of an Audit-Grade Cybersecurity Assessment
A robust cybersecurity due diligence process transcends the superficiality of administrative checklists, which often fail to capture the latent vulnerabilities inherent in complex digital ecosystems. Relying on “paper-based” self-disclosures is a perilous strategy; research indicates that 87% of Chief Information Security Officers admit their internal reporting may inadvertently minimize legacy technical debt during acquisition talks. For high-value transactions, we demand an empirical verification of the target’s digital perimeter. This rigorous methodology merges deep-tissue technical scans with executive-level governance reviews to ensure that what’s presented in the data room aligns with the reality of the server room. Legal scholars at the Harvard Law School Forum have correctly identified cyber-posture as a key risk factor in mergers and acquisitions, particularly when considering the potential for post-closing liability and the erosion of shareholder value.
Central to our investigative framework is the concept of Instrument Integrity. This principle dictates that digital access must never compromise the underlying financial instruments or the proprietary algorithms that drive their performance. It’s not enough to secure the network; we must verify that the data supporting the valuation is untainted. Our partners often seek bespoke risk advisory services to ensure their capital remains insulated from these systemic shocks, moving beyond simple compliance toward true operational resilience.
Governance and Risk Frameworks
We begin by evaluating the target’s internal security culture, focusing on executive accountability rather than just IT-level task management. We audit the maturity of existing frameworks, such as the NIST CSF 2.0 or ISO 27001, to determine if security is a board-level priority or a neglected line item. In 2023, the average cost of a data breach reached $4.45 million, making the adequacy of cyber-insurance policies a critical focal point. We scrutinize specific coverage exclusions, particularly those related to state-sponsored actors or “acts of war,” which can leave a firm exposed during geopolitical instability. This level of scrutiny ensures that the target’s risk management isn’t just a static document but a living, funded mandate that protects institutional alpha.
Technical Resilience and Defensive Capabilities
The technical investigation shifts focus toward the architecture of network defenses and the rigor of data encryption standards. We don’t just ask if data is encrypted; we verify the cipher suites used and the lifecycle management of cryptographic keys. Evaluating a target’s incident response readiness requires reviewing historical breach recovery performance, looking for patterns of remediation rather than just isolated patches. Supply chain integrity is equally vital, as 62% of system intrusions now originate through third-party dependencies. We map these external connections to ensure that a vendor’s weakness doesn’t become our client’s liability. This granular approach provides the precision required to maintain the high standards of Swiss financial excellence in an increasingly volatile digital landscape.
Translating Cyber Risk into Deal Valuation
The valuation of a target entity is no longer a mere reflection of historical cash flows and EBITDA multiples; it’s increasingly a function of digital resilience and technical debt. We categorize critical security deficiencies as unfunded liabilities that reside quietly on the balance sheet, waiting to materialize as post-close capital expenditures or regulatory fines. These liabilities represent a guaranteed future cash outflow that the target has failed to account for in its internal financial reporting, necessitating a rigorous adjustment to the enterprise value.
Quantifying these risks requires an institutional-grade approach to cybersecurity due diligence, where technical vulnerabilities are converted into hard currency figures. If a target’s network architecture is found to be porous, the cost to re-engineer that infrastructure must be deducted from the purchase price. This ensures that the acquirer doesn’t pay a premium for a digital asset that requires immediate, multi-million dollar reinvestment to meet basic security standards. Our methodology treats these findings with the same gravity as environmental liabilities or pending litigation, ensuring the investment’s entry price reflects its true risk-adjusted state.
Cyber-Findings as Negotiation Levers
When cybersecurity due diligence reveals systemic weaknesses, such as a history of undetected lateral movement or insufficient encryption of sensitive data, these findings transition from technical observations to primary negotiation levers. We distinguish between remediable risks, which are manageable through post-close investment, and deal-breakers, such as a complete compromise of the target’s core intellectual property. A high-risk cybersecurity score, as validated by institutional-grade audits, can mandate a 5-10% valuation discount to offset the inherent financial exposure of the target.
These findings provide the evidence base required for aggressive Purchase Price Adjustments (PPAs) and the structuring of protective financial instruments. For instance, evidence of substandard data governance often leads to the demand for larger escrow holdbacks, frequently ranging from 15% to 20% of the deal value, to cover potential indemnification claims. By defining specific indemnity caps around cyber-incidents, we ensure that the seller retains the risk for any “sleeping” breaches that occurred prior to the transaction date.
Protecting the Investment Thesis
Protecting the investment thesis requires a granular assessment of how the target’s digital infrastructure will support the planned post-merger integration (PMI). If the target’s systems are incompatible with the acquirer’s security standards, the anticipated synergies from data consolidation and operational streamlining will be delayed. Such delays, often extending from 12 to 18 months, directly erode the projected alpha generation of the deal. We assess the integrity of the target’s digital core to ensure it can withstand the rigors of rapid scaling without collapsing under the weight of modern threat vectors.
Day 1 remediation costs are a critical component of the ROI analysis and must be factored into the final bid. A strategic framework for these costs includes:
- Immediate deployment of Endpoint Detection and Response (EDR) tools across all legacy nodes within the first 24 hours.
- Credential resets and the enforcement of multi-factor authentication for 100% of privileged accounts to prevent unauthorized access.
- Bespoke security training for the entire workforce, targeted at mitigating the human risk factor that often leads to phishing-based breaches.
By integrating these costs into the initial financial model, we maintain the long-term stability of the investment programme. This level of precision prevents the “synergy trap,” where the cost of securing the target’s assets consumes the very profits the acquisition was intended to create.
The Swiss Alpha Matrix Approach: Beyond Automated Scans
Standard security ratings provide a surface level veneer that often obscures deeper structural vulnerabilities. While automated tools offer a baseline, they lack the intellectual depth to identify the sophisticated obfuscation techniques employed in high-stakes transactions. Our firm rejects the industry’s reliance on passive scanning; instead, we deploy executive led intelligence that scrutinizes the human and architectural layers of a target company. In the 2023 fiscal year, 64% of high-value M&A targets exhibited “green” health scores on automated platforms despite harboring critical backdoors in their legacy infrastructure. This discrepancy highlights why a purely digital approach is insufficient for institutional capital preservation.
The Wise Guardian philosophy serves as our operational compass. We treat every cybersecurity due diligence engagement as a fiduciary responsibility, prioritizing the long term stability of your portfolio over the mere completion of a deal. Our methodology relies on on-ground verification, particularly in cross-border acquisitions where digital data trails are frequently manipulated. During a 2023 acquisition involving a Southeast Asian logistics firm, our team identified a 12% discrepancy between reported server logs and physical hardware configurations. Such precision prevents the inheritance of “toxic” technical debt that can erode alpha long after the ink has dried on the contract.
Discretion remains the cornerstone of our Swiss heritage. In the sensitive environment of an M&A news cycle, even a minor leak can trigger market volatility or alert adversarial actors. We maintain Swiss grade confidentiality through air-gapped reporting and encrypted communication channels that exceed standard institutional requirements. This quiet authority ensures that our investigations remain invisible to the market, protecting the integrity of the negotiation process at every stage.
Independent Verification of Financial Systems
We provide rigorous validation of bank-grade systems and financial instrument communication channels, specifically focusing on the integrity of ISO 20022 messaging standards. Our experts detect sophisticated social engineering schemes that targeted 71% of global C-suite executives in the Q4 2023 reporting period. By operating directly in financial hubs like Hong Kong and Geneva, we verify the physical and logical security of the systems responsible for moving capital. This localized presence allows us to confirm that financial data hasn’t been intercepted or altered by sophisticated regional threat actors.
A Bespoke Mandate for Every Transaction
One-size-fits-all cyber tools fail in complex, multi-asset programmes because they ignore the unique risk profile of specific jurisdictions. We tailor the depth of our cybersecurity due diligence to the specific nuances of the deal, whether it involves a sovereign wealth fund or a private equity carve-out. In 2022, 43% of failed integrations were attributed to unforeseen technical incompatibilities that automated tools missed. Our process ensures a seamless transition from initial investigation to ongoing strategic project oversight, maintaining the security posture of the asset throughout its entire lifecycle.
Secure your next acquisition with the precision of Swiss architectural oversight. Explore our bespoke mandate options
Executing the Cybersecurity Mandate: Next Steps for the C-Suite
The execution of a sophisticated acquisition strategy necessitates an unwavering commitment to digital integrity, a requirement that transcends the standard checklists of traditional auditing. When the stakes involve institutional-grade assets, the integration of cybersecurity due diligence into the earliest stages of the transaction lifecycle isn’t merely a defensive measure; it’s a strategic imperative that secures the long-term viability of the investment. Proactive leaders initiate these assessments during the initial target screening phase, rather than treating them as a late-stage confirmatory exercise. This early involvement allows for the identification of systemic vulnerabilities that can impact final valuations by 15% to 20%, as evidenced by several high-profile technology sector devaluations in 2023.
To maintain absolute objectivity, the C-suite must appoint independent advisors who operate outside the influence of sell-side disclosures. This separation ensures that the assessment remains untainted by the inherent conflicts of interest found in vendor-provided reports, which often prioritize the optics of a seamless exit over the granular reality of technical debt. A robust cybersecurity due diligence framework ensures that capital deployment decisions are backed by empirical evidence rather than optimistic projections. Key actions for the executive team include:
- Mandating independent technical audits: Relying on the target’s internal reports is a risk that institutional investors can’t afford to take.
- Codifying remediation roadmaps: Findings must be integrated into the final definitive merger agreement, utilizing holdback escrows or specific indemnity clauses to address identified risks.
- Quantifying potential liabilities: With the 2024 IBM Cost of a Data Breach Report citing an average cost of $4.88 million per incident, these figures must be factored into the risk-adjusted return calculations.
- Implementing continuous monitoring: Establishing a post-deal surveillance programme protects capital during the high-risk transition period, specifically during the first 100 days of IT infrastructure integration.
Decision-making must be precise. By incorporating these remediation roadmaps directly into the legal framework of the deal, the acquiring entity creates a mechanism for accountability that persists long after the closing signatures are dry. This structural approach mirrors the traditional discretion and meticulousness of Swiss financial traditions, prioritizing the preservation of wealth through rigorous, unemotional analysis.
Selecting the Right Advisory Partner
Identifying an advisory partner requires a rare synthesis of Tier-1 investment banking acumen and deep technical forensics. The ideal partner possesses a global reach that enables on-ground verification in diverse jurisdictions, ensuring that bespoke mandates are executed with the same precision in Zurich as they are in Singapore. This institutional-grade approach ensures that your strategic growth isn’t compromised by invisible digital liabilities. Consult with Swiss Alpha Matrix for your next high-stakes mandate to ensure your capital is managed with the quiet authority it deserves.
Securing Deal Integrity
The final word on transactional success rests on the ability to merge financial discipline with audit-grade validation. By establishing a continuous monitoring programme, the C-suite ensures that the integration of disparate IT environments doesn’t create new apertures for threat actors during the critical post-deal phase. This methodology transforms cybersecurity from a technical hurdle into a pillar of transactional excellence, allowing for the confident pursuit of alpha in an increasingly complex global market. Explore our Complex Project Management and Due Diligence services to witness how Swiss discretion meets modern strategic architecture.
Fortifying Enterprise Value through Strategic Digital Oversight
The integration of robust cybersecurity due diligence into the M&A lifecycle represents a fundamental shift from technical check-boxes to strategic value preservation. Since global transaction volumes are projected to reach $5.2 trillion by the close of 2026, the margin for error in digital risk assessment has effectively vanished. Executives must prioritize audit-grade instrument validation that transcends superficial automated scans. This ensures every vulnerability is quantified within the context of deal valuation and long-term asset integrity.
Swiss Alpha Matrix brings a unique pedigree to this high-stakes environment. Our methodology is led by former Tier-1 global bank executives who apply the same rigor to digital assets that they once applied to institutional capital market transactions. We provide on-ground verification and Swiss-grade discretion across complex cross-border mandates. It’s this level of precision that’s required for institutional-grade decision making. We transform latent risk into a measurable component of alpha generation.
Secure your next transaction with institutional-grade due diligence
We look forward to safeguarding your firm’s strategic growth and ensuring your capital remains protected in an increasingly complex global landscape.
Frequently Asked Questions
What is the difference between a standard IT audit and cybersecurity due diligence?
An IT audit evaluates the operational efficacy of hardware and software, whereas cybersecurity due diligence assesses the latent risks that threaten the integrity of the deal’s valuation. While a standard audit might confirm that 95% of servers are operational, our investigative process scrutinizes the 5% of unpatched vulnerabilities that could lead to a $4.45 million breach, the global average cost identified in 2023. We prioritize the preservation of long-term alpha by identifying systemic weaknesses before capital is committed.
How long does a comprehensive cybersecurity due diligence process typically take?
A rigorous investigation typically requires a duration of 21 to 45 business days to ensure absolute technical accuracy. This timeline allows our experts to conduct a multi-layered analysis of the target’s digital infrastructure, including deep-web scans and historical breach forensics. We don’t rush these mandates; the complexity of global financial markets demands a measured pace that guarantees a 100% thorough assessment of the target’s risk-adjusted profile. It’s a structured approach that mirrors the precision of Swiss financial traditions.
Can cybersecurity findings actually stop a merger or acquisition from proceeding?
Cyber findings frequently lead to deal termination or significant price renegotiations, as evidenced by the $350 million valuation reduction in the 2017 Yahoo acquisition by Verizon. If our team uncovers structural flaws that jeopardize the target’s intellectual property, we provide the strategic evidence necessary to halt the transaction. Our role as a Wise Guardian ensures you don’t inherit a liability that compromises your institutional-grade portfolio’s stability. We focus on protecting your capital from the volatility of unmitigated digital threats.
How do we quantify the cost of remediating a target’s cyber-vulnerabilities?
We quantify remediation costs by aggregating technical debt and projected incident response expenses based on the 2023 IBM Cost of a Data Breach Report. By assigning a specific dollar value to each vulnerability, such as the $165 average cost per compromised record, we create a bespoke financial model. This precision allows for the integration of these costs into the final purchase price; it ensures that your strategic growth isn’t undermined by unforeseen capital expenditures or technical deficiencies.
Is cybersecurity due diligence necessary for smaller, non-tech acquisitions?
Every acquisition requires cybersecurity due diligence regardless of industry, because 98% of global organizations maintain connections with at least one third party that has suffered a breach. Non-tech firms often possess less mature defenses, making them attractive entry points for sophisticated threat actors. We apply the same Swiss precision to a mid-market manufacturing firm as we do to a global fintech entity. This protects your multi-asset diversification strategy from the cascading effects of a supply chain compromise.
What role does cyber-insurance play in the due diligence process?
Cyber-insurance serves as a critical risk-transfer mechanism that necessitates a high level of institutional hygiene before a policy is underwritten. Insurers now demand evidence of Endpoint Detection and Response implementation, which can reduce annual premiums by approximately 20% for firms meeting these benchmarks. We evaluate the target’s insurability to ensure that the post-acquisition entity maintains the requisite coverage. This protects against catastrophic capital loss and aligns with our commitment to excellence and long-term wealth preservation.
How does Swiss Alpha Matrix ensure discretion during high-profile M&A investigations?
Swiss Alpha Matrix maintains discretion through the utilization of air-gapped forensic environments and Tier 4 data centers that adhere to the highest Swiss banking standards. Our communication protocols involve encrypted channels where access is restricted to a selected group of senior partners. We prioritize your privacy, ensuring that high-profile investigations remain confidential while we build the intricate, multi-layered defense strategies required for your bespoke mandate. It’s a standard of service that is both global in reach and local in its attention to detail.
What are the most common cyber ‘red flags’ found during the due diligence phase?
The most frequent red flags include unpatched legacy systems and the absence of Multi-Factor Authentication across 75% of administrative accounts. We also identify a lack of incident response planning as a primary concern, given that 80% of successful breaches involve the exploitation of compromised credentials. These indicators suggest a fundamental lack of institutional excellence. They signal that the target’s internal controls aren’t aligned with the standards of a sophisticated investor who values stability and strategic precision.